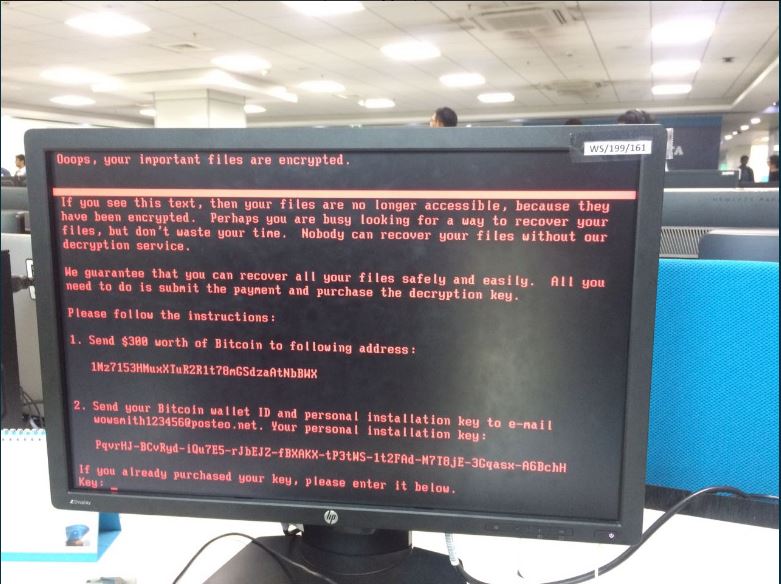
Yup, its only been one month since the WannaCry cyber attack was stopped and we already have a second go at a similar attack.
This new ransomware, dubbed Petya or Petrwrap, is targeting businesses and governmental institutions around the world. Reports indicate that the attacks started in Ukraine which later spread to Spain, France, Russia and India, with Ukraine’s Oschadbank and Russia’s Rosneft bank among the victims.
Some of our gov agencies, private firms were hit by a virus. No need to panic, we’re putting utmost efforts to tackle the issue 👌 pic.twitter.com/RsDnwZD5Oj
— Ukraine / Україна (@Ukraine) June 27, 2017
Well, even some Point of Sale systems have felt the pinch this time:
Unpatched PC's were hit again by #Petya #ransomeware.
POS, Banks, ATMs, Airport, GOV, Media companies, Metro, Cargo, Post…#Eternalblue pic.twitter.com/4n0VosQDuz— Lukas Stefanko (@LukasStefanko) June 27, 2017
According to Symantec, Petya is using the same EternalBlue exploit that was used by WannaCry to spread. Reports also indicate that Petya is a well-known software that is offered as a RaaS (Ransomware as a Service) software on the dark web.
Petya was known to be RaaS (Ransomware-as-a-Service), selling on Tor hidden services. Looks like WannaCry copycat. Attribution will be hard. pic.twitter.com/W5voMeNx9I
— x0rz (@x0rz) June 27, 2017
Unlike WannaCry, the situation seems to be less detrimental this time however, at the time of this article, around 35 payments had been made to the Petya Bitcoin account, totaling to around $8,988.
The bitcoin wallet tied to #Petya/#NotPetya ransomware has so far received 35 payments totaling 3.51681746 BTC ($8,988.61 USD)
— petya_payments (@petya_payments) June 28, 2017
According to a McAfee executive, the payments are likely to be from security researchers but still warns against paying the ransom, as it is not a gurantee that a decryption key will be provided by the attackers.
“We saw this with WannaCry; there are so few people that are making the payments,” said the MaAfee executive. “I think the message of ‘don’t pay’ seems to be getting through.”
However, security researchers have a theory that these attacks have more to it than just the few dollars they get from the “ransom”. The attacks look like ransomware but it seems like that is not their main intention.
Similar to WannaCry, the payment process of #Petya looks like shit. Are they really financially motivated? 🤔 #ransomware
— x0rz (@x0rz) June 27, 2017
This second wave of attack is a clear indication that governments and other institutions do not take cyber security seriously, even after the WannaCry attack. I am particularly worried about the Kenyan government, who already have a spamming problem.
Read More: Official Kenya Government Emails Used to Send Out Spam Messages